CloudTrail insights and monitoring in 5 easy steps!

Know Better®
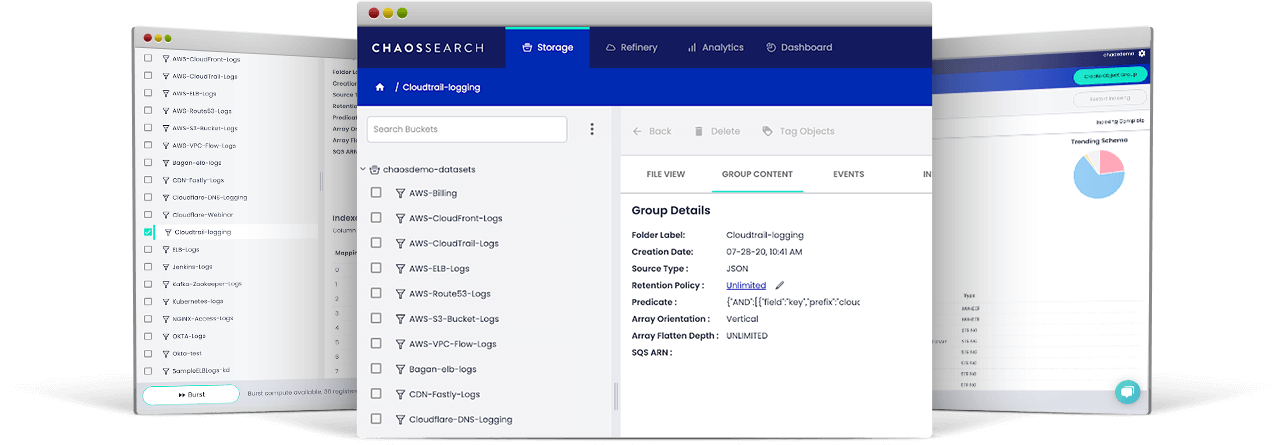
ChaosSearch takes a new approach to dramatically increase your ability to monitor and analyze data at scale while simultaneously reducing the operational costs of text search and relational analytics. We created the new UltraHot® universal data format (index) and associated architecture, which allow for direct and accelerated analytics on cloud object storage.
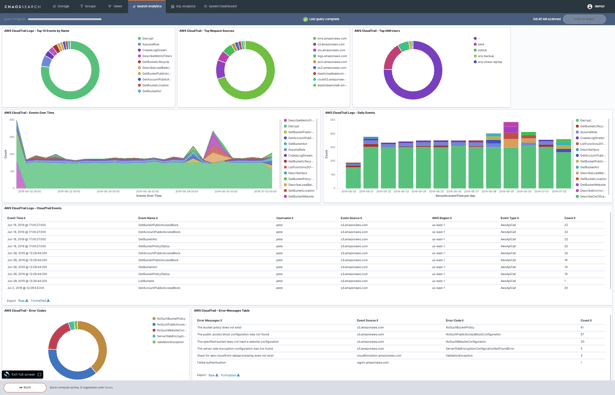
Monitoring and analyzing activity within your AWS environment can be extremely difficult at best and a nightmare at worst. This is why AWS offers their CloudTrail auditing service, an API logging tool that stores a record for every service call that occurs anywhere within your AWS account. CloudTrail enables complete visibility into the activity that occurs within your account, enabling you to see exactly who did what, when, and where.

Monitor
Anomalous activity from users and services.
Search
Years worth of data within just a few minutes.
Analyze
Long running services, top events and unusual activity.
Monitoring Top Services
For both resource consumption (cost) and user activity monitoring (UAM)



Discover and Catalog CloudTrail Events Faster Than Ever Before!
©2024, ChaosSearch®, Inc. Legal
Elasticsearch, Logstash, and Kibana are trademarks of Elasticsearch B.V., registered in the U.S. and in other countries. Elasticsearch B.V. and ChaosSearch®, Inc., are not affiliated. Equifax is a registered trademark of Equifax, Inc.





